
Artificial intelligence is changing credit cards and banking
Industry: Artificial intelligence
Some major credit card providers, however, are using artificial intelligence to make it easier to not just choose your rewards, but offer the rewards consumers want the most. In this drive for hyper-personalization of our rewards, artificial intelligence banking is benefiting all parties involved.
Deployed by major banks including HSBC and Bank of America, AI and predictive analytics make it easier for banks and loyalty program issuers to determine what rewards consumers will want at any given time and offer those rewards, along with incentives to use their card for future, similar rewards.
AI makes that kind of hyper-personalization possible, so you get more relevant rewards that you're more likely to use, delivered proactively – before you even realize you want to redeem the rewards you've accrued.
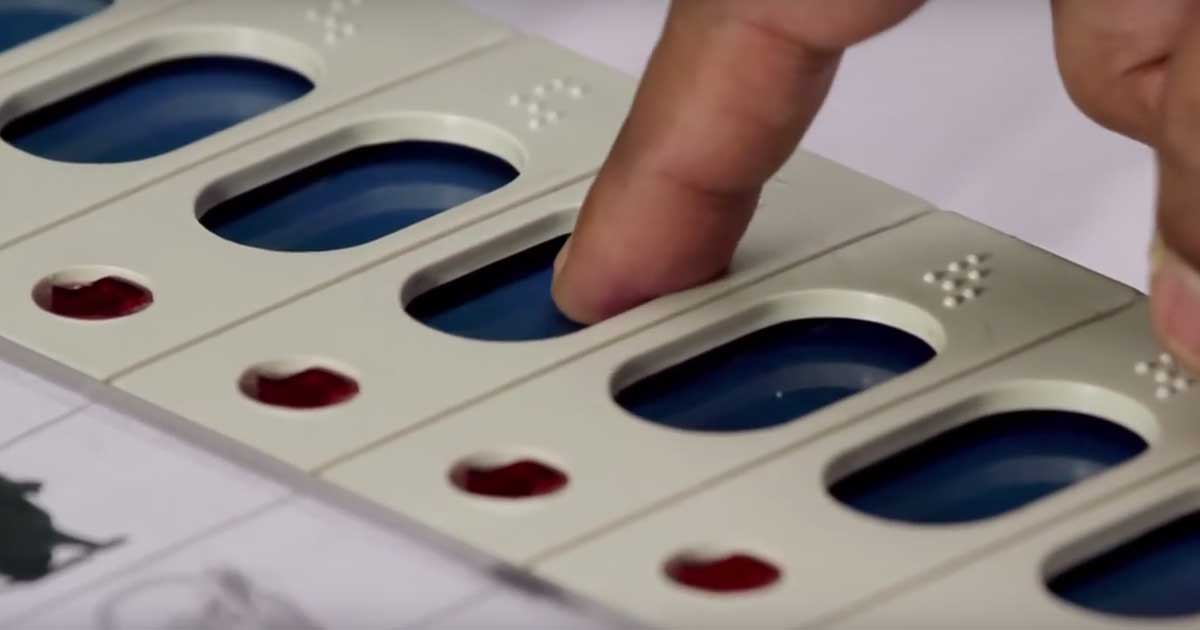
The many claims of EVM tampering in India. What has happened?
Industry: EVM
Less than three months before the parliamentary elections, the Europe chapter of the Indian Journalists' Association (IJA) was set to demonstrate how electronic voting machines (EVMs) can be hacked.
Syed Shuja, a US-based cyber expert who claims he was a part of the team which designed Electronic Voting Machines (EVMs) used in India, alleged that the 2014 general elections in India were rigged and that senior BJP leader Gopinath Munde was murdered because he knew about the tampering. However, there are some massive loopholes in his explosive claims.
He claims that the tampering can be done using a modulator to tap into a low frequency. He also claimed that the modulator was of “military grade” and was sold to Reliance between 2012-2014. He also could not be clear if he was accusing Reliance Communications or Reliance Jio in the process. But he later said that it was a Mukesh Ambani company. This is something that can be looked into but he did not provide any evidence to his claims.
The Election Commission rejects charges of EVM hacking in 2014 polls and said EVMs used in Indian elections were manufactured by Bharat Electronics and Electronics Corporation of India under “very strict supervisory and security conditions”.
The election watchdog also said it was mulling legal action in response to the claims made by a person identified as Syed Suja at a press conference in London.

Indian govt exploring ways to exempt security agencies from Data Protection Bill
Industry: Data Security
The government is in a last mile huddle with security and intelligence agencies to find ways to either exempt them from the Personal Data Protection Bill or put in place a special dispensation to regulate their public scrutiny.
Some of these agencies, sources said, have suggested a blanket exemption as in Section 24 of the Right to Information Act. Some others have pointed to the model followed in the IT Act under which 10 agencies were recently designated as authorities empowered to intercept digital traffic through a laid out approval process. Another view being explored was to have an oversight mechanism to prevent misuse by intelligence agencies.
The proposed Personal Data Protection Bill requires entities to obtain consent of individuals before accessing their personal data, which intelligence agencies argue is counterproductive to their mandate of monitoring activity for security purposes. Also, they add surveillance under these provisions will leave them legally vulnerable. Moreover, the Bill does not distinguish between government and private entities.

How IoT is keeping the story alive for IT services companies in India
Industry: IoT
Technology services companies are likely to see IoT services market grow two-and-a-half times to $270 billion in five years (by 2023) from $106 billion now.
IoT services - which include business opportunities such as strategy & consulting, engineering, IoT system integration & deployment, and managed services & support - have seen 28% growth year-on-year fuelled by demand from across healthcare, retail, automotive and industrial fields.

When Is the Time to Hire a Cyber Specialist?
Industry: Cyber Security
Even though the topic itself is increasing in importance, it remains a truism that many smaller organizations (and in fact, some mid-sized ones) don't have specialized security expertise on staff.
When responsibility is distributed among multiple individuals -- or when responsibility is otherwise unclear -- important security-relevant tasks can slip through the cracks. Designating someone, clearly and unambiguously, helps control this.
It helps defuse conflicts of interest. Sometimes appropriate security due diligence means pushing back on otherwise-valuable activities. When an individual's job includes both security and something else in equal measure, situations can arise when that person will need to choose one role over the other.
Details: https://www.technewsworld.com/story/85682.html

Digital India firewalls: look-alike domains, frauds big threats to govt's e-push
Industry: Cyber Security
The government's Digital India push is now running into a firewall of tech-savvy fraudsters.
The ministry has identified at least six common hi-tech modus operandi being increasingly employed. These include using names similar to government schemes to create phishing websites, using the logo of government schemes with photographs of Prime Minister Narendra Modi and Cabinet ministers to add authenticity, providing link of government sites to display affiliation to the Central government, alluring common people by promising government jobs by issuing fake appointment letters and extorting money and targeting newly-launched government schemes and trapping people because of lack of awareness.