6 Popular Cyber Security Myths busted
Article: Cyber Security

While the organizations are going gaga over implementing cyber security framework, there are half truth and bizarre myths that are floating around. The picture is quite scary if we look at the media. Every day, we hear stories about security breaches and ransom ware attacks that are crippling organizations. Data leaks and identity theft are also affecting innumerable number of people.
Cyber criminals are coming up with more sophisticated attacks which can cause permanent destruction of data as we have seen in Petya and Wannacry attacks this year. As much as hackers are polishing their skills, organizations too should strive to remain one step ahead of them.
Above all, there are few myths about cyber security which must be busted right now. Otherwise, it may lead to wrong assessment of threats, misallocate resources and set inappropriate goals. It is very important to separate the facts from fiction.
To fight against cyber criminals, the most effective and valuable weapon is our own mindset. Let's see what are the myths going round and how can we deal with them:
1. Cyber Security is the concern of IT department
In any organization, the first line of defense is the people at the time of any cyber-attack and securing sensitive information is the responsibility for everyone. The biggest problem, the organizations face is how and where the information is kept. Marking online threats as the only concern of IT department multiplies the effectiveness of the attack.
"Once information is digitized, everything from accuracy, privacy, availability to integrity to be protected." Where phishing attacks are the most common way to trap users, it will be difficult to protect company data with the lack of knowledge of the employees. So, educating staffs other than just IT department should be a primary concern for organizations. That’s why cyber security has now become an issue that is handled at boardroom level.
2. Security Software is good enough to protect data
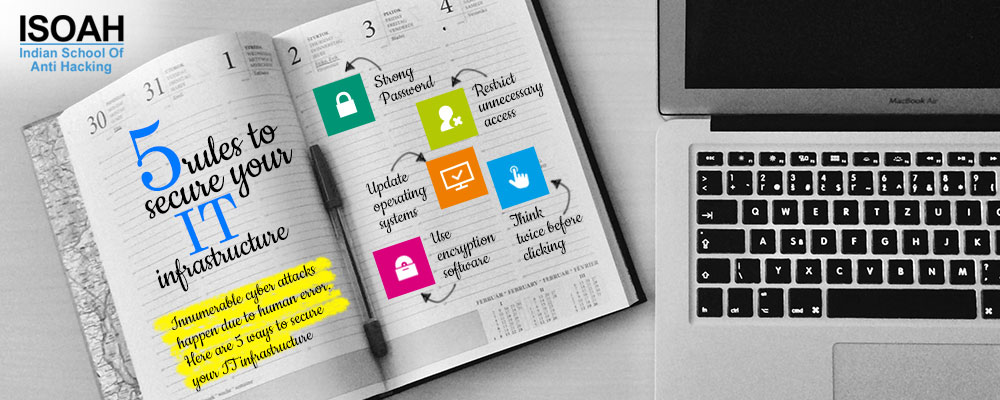
Almost all grave security breaches had security solutions and firewalls deployed. Some of them had next gen technologies. Then how did the breach take place? The fact is, managing and installing good security software is the first step to implement cyber security but definitely not the sole key to ensure it. Security software is effective in reducing the cyber risk and mitigating its effect. Again introducing complex technical solution which is unusable by staff would be counterproductive. People pose as the biggest threat when it comes to securing information. A lot of hacking attempts and security errors are due to human error. People often click a malicious links or download suspicious attachments without realizing the consequence.
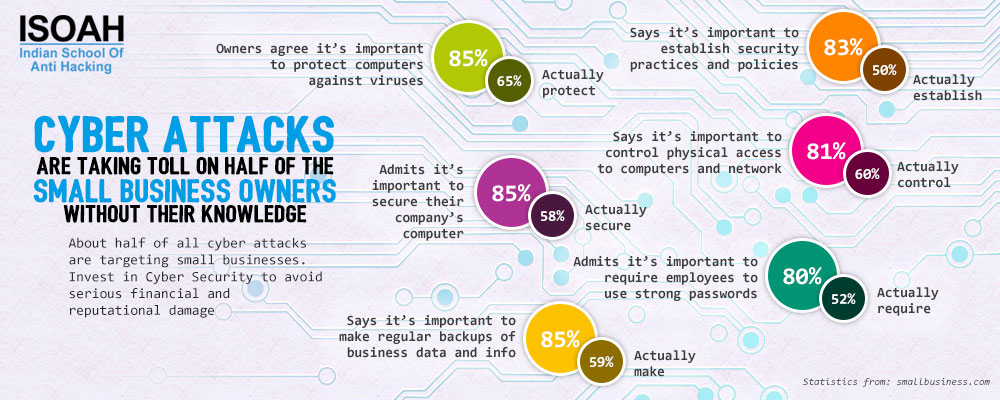
3. Only the big business houses get attacked
The biggest assumption they make, nobody will be interested to steal data from a small business house. A 2015 HM Government report confirmed that 74% of small and medium-sized enterprises reported a security breach. However, only 7% of small businesses expect information security expenditure to increase in the next year (www.itproportal.com). The reality is, small business houses are often the soft target for hackers as they know, the need of implementing proper cyber security measures mostly been ignored there. They know the fact that less is being done to protect data. Whereas, small businesses too have sensitive data about clients, bank details etc which must be protected.
4. IoT can alone battle with security risks
Most of us believe that artificial intelligence will make our lives easier. It is true that IoT is capable of analyzing massive data pools and in case of security the technology can detect and analyze threats. It seems like a huge step forward allowing individuals to control different gadgets from a remote distance with mere internet access. But it is actually making it easy for the criminal as well. Now the attacker only needs to have internet access to accomplish his/her goals. Organizations must pay attention to understand the technology and its functions to the core before using it as its primary security tech. Machine learning is an important part of layered defense system, but it can’t be exclusive.
5. Disconnecting with internet minimizes risk
Disconnecting devices can mitigate risks but it doesn't eliminate it. "But disconnection of data is a myth," said CEO and President of Identity Theft Resource Center Eva Velasquez, "unless you're a sole proprietor with one machine and left offline, it's unachievable." Disconnecting, unplugging or creating "air gaps" between devices and networks or going back to paper can actually increase vulnerability. Paper documents can easily be copied or removed. It is unrealistic to disconnect necessary technology needed to improve efficiency and quality. Meanwhile, air-gapped and disconnected networks are harder to monitor as they are not updated with the security patches often and there would be less logging of data. Organizations need to be concerned about the access of data but disconnecting from the network does not wipe off the risk.
6. The manufacturer should be concerned about safe computing, not me
Yes it is expected that manufacturers of software, hardware and other devices (routers, phones) must include some safety features. But this doesn’t mean your safety is guaranteed. Manufacturers understand that security is important and are working to improve it. For example, Windows 10 is widely accepted for its security features and regarded as the most secure Microsoft operating system. But the challenge is, if a computer is too secure, users often avoid using it. And they try to find a less secure way to access information.
People also tend to believe that malicious software and viruses only affect computers and laptops which are not true at all. Phones are equally vulnerable. Mobile malware affecting smartphones, tablets and other devices have increased by 58% than last year (http://www.hackademic.in). Malwares can steal information like contact number, email id and use phone's GPS to track users. In fact, one can get affected by social media sites as well through gift cards and survey scams.
There is nothing like perfect security. Nobody is immune from cyber-attacks. Cyber security must be dealt from a prevention-first mindset. To have total confidence on security measures and devices can prove equally unwise. So, we need to be very cautious to safeguard our privacy while using computer or phone. Cyber crimes happen largely due to human error and social-engineering attacks. We need to educate ourselves to avoid the damage caused by cyber attacks with more awareness and alertness. Since software and networks can have security patches but not the human mind!