Biggest cyber security risks involved with IoT - How to diminish them?
Article: IoT
We are living in a world full of interconnected devices. The technical innovations of course opening the doors for more cool and convenient lifestyle as it is becoming easy to keep remote things at your fingertip no matter where you are. The flip side of this whole technical sophistication is that anything connected to the Internet is potentially vulnerable.
With IoT, the world essentially becomes one integrated information system aimed at improving the quality of life and driving new business models. As IoT creeps into every aspect of our existence, many security issues arise and the network that may just connect the home could pose a threat to the general public if compromised.
Currently, more things are connected to the Internet than people. According to an infographic from Cisco. It goes on to say that 25 billion devices are expected to be connected by 2015 and 50 billion are slated to connect by 2020. The study also showed that 70 percent of IoT devices contain serious vulnerabilities.
Cloud Security & IoT:
IoT attacks can afflict the public and cause severe disruption. Many companies have embraced the potential of cloud systems to store their databut it raises the spectre of who exactly can access that data and through which devices, all of which will be IoT-capable. It is always feasible for criminals to gain access to a company's records than to hack a microwave. They can monetize the information available in the cloud and sell them on.
Numerous IoT enabled devices in a network:
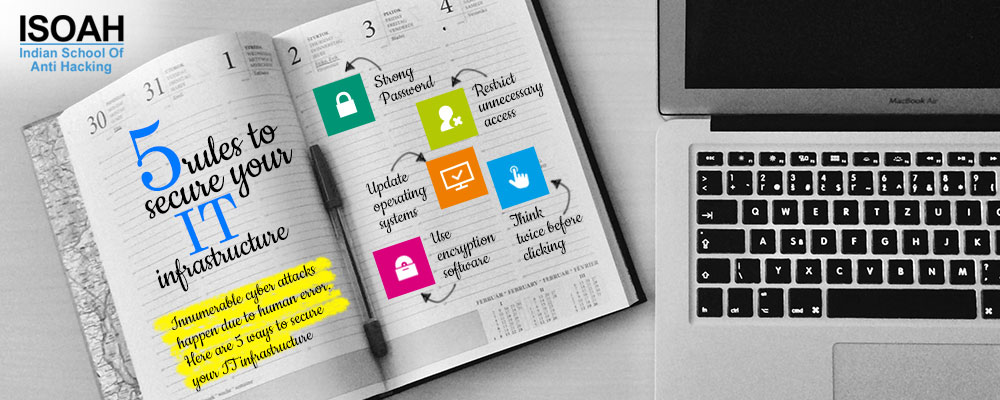
Beyond data breaches, a network comprising numerous IoT-enabled devices also puts the business itself at risk since hackers may penetrate the system and subject a corporation to sustained attacks, like DDoS'ing. To safeguard against this, it is imperative that companies regularly update and patch their systems on the one hand and properly brief their employees as to correct procedure with regard to IoT-enabled devices on the other. Letting the workers to connect their own devices to the network could provide an opportunity for attack.
IoT complexity magnifies cyber risk:
In the one hand, IoT is a technological marvel that represents the new height of human ingenuity, but on the other, it relies on a host of advanced technologies that might not always work exactly as they are supposed to. By connecting a greater diversity of devices to networks, this brings with it the associated risks. Security of each node in the framework is necessary to impart security as a whole. Organizations need to have a control system in place for unauthorized devices connection. All connected devices need to adhere to security protocols in place to ensure full security integration across all nodes.
Insecure mobile interface:
Mobile devices have become a professional necessity. As the applications and functionality of mobile devices expand, so does its usage. As such, companies now include such devices into its Information Technology strategy as a pivotal component integrating corporate cyber security and data safety policies. Here, weak authentication or unencrypted data channels can allow an attacker access to the device or underlying data of an IoT device that uses a vulnerable mobile interface for user interaction. Security vulnerabilities can lead to various issues like, account enumeration, no account lockout, exposure of credentials in network traffic. The entire system, including mobile devices, need to be incorporated into security procedures.
Public safety & IoT:
Vulnerabilities in the network services that are used to access the IoT device might allow an intruder to gain unauthorised access to the device or associated data. A compromised network not only allows access to private banking details, but access to public infrastructures such as traffic lights, GPS tracking systems, water services and power plants could fall prey to hackers. Thus a compromised system has greater consequences than organizations losing profitability and efficiency. With additional firewall, network traffic monitoring and access control - security of all interfaces like mobile, cloud, fixed should be maintained.
Data volumes & IoT:
A Federal Trade Commission report stated that 10,000 households can generate 150 million data points daily which provides a significant number of entry points for hackers. The proliferation of IoT has enabled the collection of big data. Intelligent processing and analysis of this Big Data is the key to developing smart IoT applications. Smart sensors gather information for use in machine learning algorithms to add value to businesses and promote informed decision making. It is obvious that the volume of data generated from IoT devices is immense. It is advisable for companies to employ experts to ensure secured networks and devices against unwanted infiltration.
Capable hackers are everywhere and their growing focus on the IoT is a natural progression since they are looking to where the world's data is flowing. The interconnected world is coming, but so are its hackers. But IoT is not all bad. There is also a growing swell of increasingly sophisticated device management, encryption, access control and other solutions that should make distributed architectures as safe as practicable without inhibiting data and service functionality. IoT devices have great potential to make our lives easier. However, the security issues must be considered and addressed, otherwise the devices could lead to a lot more trouble than they are worth.