Insider Threat: The biggest security nightmare of a company
Article: Cyber Security

What is insider threat? How to detect it? How would you deal with it? Know your cyber enemy inside out!
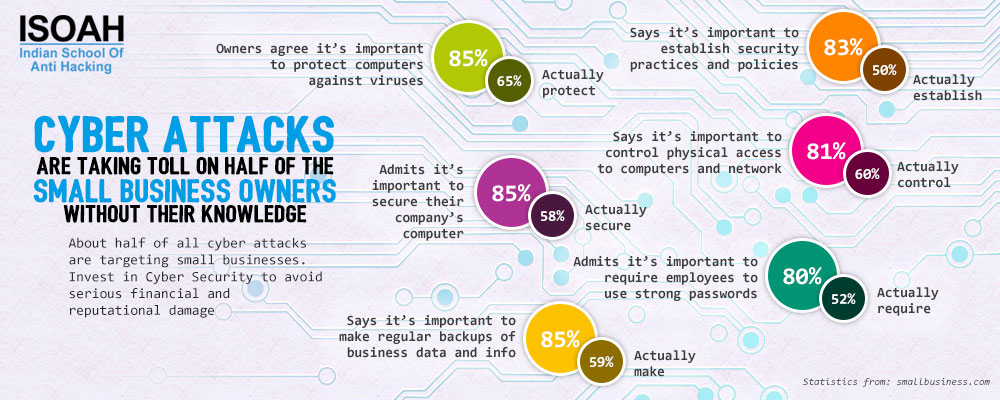
We are living in an age when businesses and consumers are equally suffering from data breaches, ransomware and many other forms of cyber attacks. As data is becoming one of the most valuable currencies, everyone is after it and people can go to any extent to make money out of it; even your own employee.
According to 2017 Cost of Data Breach Study, Ponemon Institute, it takes approximately 191 days for companies to identify that they have been breached. Have you ever wondered how is it possible for attackers to stay hidden for so long? Your own employees can inadvertently compromise your data and cost your company tons of money.
An insider attack is defined as a crime perpetrated by or with the help of a person working for or trusted by the victim. An insider attack is often accomplished by the persons who have access to private information about the organization’s operations. The engineer, Anthony Levandowski, who made Google a world leader in self-driving cars, was accused of stealing its secrets and taking them to Uber. He was accused of stealing 14,000 confidential files about Waymo’s (formerly Google’s self-driving car unit) self-driving technology including detailed designs of proprietary circuit boards and the laser ranging LiDAR systems when he was employed there.
Why are Insider Threats so hard to deal with?
- Insider threats are difficult to detect. A breach can go undetected for years, and the longer a company takes to detect it, more remediation cost they need to bear.
- Employees are allowed to handle sensitive data, as they require such access to serve their function. So it is very tough to detect whether they are up to anything malicious activities or not.
- Any tech-savvy employee would easily be able to cover their actions by editing or deleting logs to conceal the malicious actions.
- Employees can easily get away with it by admitting that it was just a mistake. It is almost impossible to prove guilt in such cases.
Furthermore, as employees already have user accounts and corporate email addresses, they already know which data is of particular value to the organization. According to 2017 Insider Threat Report, 74% companies feel that they are vulnerable to insider threats.
But what might be the cause of it?
It should be noted that the ‘insider threat’ must not necessarily be a ‘rogue administrator’. A loyal employee or stuff, fell foul to a social engineering exercise can leave the company open to attack because he had more access than needed. While changing the job role, the removal of the old access is frequently overlooked. Likewise, when someone leaves the company, their account does not get revoked in a timely fashion, once more leaving a vulnerability that is relatively simple to fix.
In case of a data leak, one should pay attention to three groups:
- Privileged users in a company are the most trusted and they have the most scope to misuse the data both intentionally and unintentionally.
- Third-party vendors, remote employees or subcontractors usually have access to the company’s data and in no way, you can check the security of their systems.
- After termination, make sure to revoke all access to that employee from company data so that they cannot access data via malware or backdoors.
How to fight with insider threats?
The prevention of insider attack includes proper allocation of account rights, the use of internal firewalls, proper user training and physical security measures.
1. Know your employee well:
While hiring, do a background check on the employee. Observe their social network profiles or call their previous employers to get all the info you need. This process will at least filter out the risky applicants. Also, observe the behaviors of the employees. If they are unhappy, try to understand what problems they are facing and talk it out.
2. Control user access:
Improper or inappropriate account rights often lead to unauthorized access. Set a proper rule for each department about how much access the department’s employees would require. The structure and allocation of account privileges should be formalized, possibly in the organization’s security policy. Prohibit credential sharing between employees and limit the use of shared accounts as much as possible. Don’t forget to use two-factor authentication as it protects your accounts by requiring a user to employ a security token or an additional device to complete the authorization. Controlling access not only prevents external threats to get in but also restrict employees from authorizing systems at odd times.
3. Monitoring User Activity:
User action monitoring tool is very easy to use. It can be used for video recording of all user sessions which might be useful for the security specialists of the company to review what users have done with the data. Apart from being a great investigating tool, these monitoring tools also provide concrete evidence to prove a data theft in front of the court.
4. Install internal Firewall:
When dealing with insider attacks, however, these same firewalls can be deployed within the internal network to protect more sensitive computers, servers, and network segments from attacks from within the network. Firewalls are generally considered to be a perimeter defense and, as such, are deployed on the perimeter of networks. The firewall should be set-up to allow only specific types of access into the protected computers. Another use of the firewall is to log any attempted attacks. This can then be used to identify any employees who may be trying to attack that specific server or network segment.
5. Educate Employees:
Employee training is a major key to prevent insider attack as they are the last line of defense for any organization. Make them aware of the dangers the company might face in case of data breach and how to deal with them. Imply certain security practices within the organization to avoid any silly security mistake. Empower the employees so that they become an asset and not a liability.