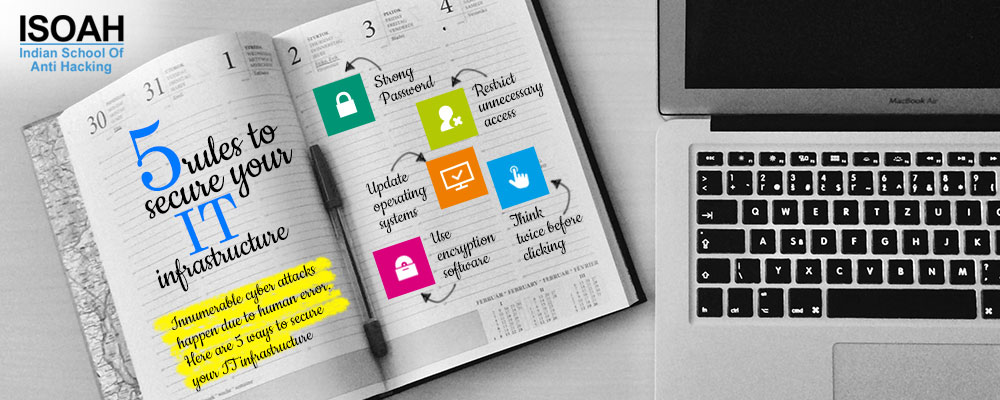
5 rules to secure your IT infrastructure
Article: IT Security
Just like charity, data security also begins at home (read workplace).
No business can flourish without its online presence. As technology has continued to be a blessing for business of every size, the doors of opportunities for fresh entrepreneurs have opened. But, just like every other thing, technology has its pros and cons too. And at this point of time, the biggest concern of business houses is protecting online data.
Every year, National Cyber Security Awareness Month is observed in October to raise awareness about cyber security. It is impossible to run a business without being exposed on internet as it touches almost every aspect of our day to day life. And there, cyber threats pose as one of the gravest security dangers across the world. Sensitive information like financial records, client details, staff details or confidential documents stored in business computers or cloud needs multi-layered approach to keep it safe. As we all know, a grave cyber attack can bring any organization to its knees by stealing sensitive information and damaging online reputation. That's why it is important to implement as many safety measures as possible in the organization, so that the hacker will look for easier targets to hit.
According to security specialists, protecting data involves three major steps: Understanding of potential threats, arranging proper layers of defense and continual monitoring. Following are the few steps to ensure data security recommended for every business house.
Strong Password:
Weak password protocols can lead to disaster for any organization. Access to wireless networks, equipments and sensitive data must be guarded with unique passwords. Passwords must contain upper and lower case letters, numbers, special characters. Avoid using easy-to-guess numbers or commonplace words from the dictionary to make it unique. If a master document is maintained with all the passwords, make sure to encrypt it with unique passcode and keep it in a secure place.
Also, do not forget to change default passwords and account names whenever a new machine or software is installed. This is a common security mistake people tend to make which can be rectified very easily.
Restrict unnecessary access:
Limiting access to your technology infrastructure can automatically reduce the chances of being exposed to hackers. Restrict individual user's or system's access only to their needed equipment or data or programs. Creating a unique set of email addresses, logins, servers and domain names for each department or user can minimize the scope of potential danger.
Do not fail to update operating systems:
Make sure all the computer operating systems are updated. Hackers are often in search of systems that lack the latest safeguards. Sign up for automatic updates that install security patches. Also, install good anti-virus software that can block spam and detect spyware immediately and never fail to use the updated version of it.
Use encryption software for most sensitive data:
Encrypting data is important to protect client's financial information as well as company's internal information like personal files, financial records and product details etc. To run the online operation smoothly, a company must look into encrypting files which fairly secure sensitive data.
Think twice before clicking:
Beware of phishing scams. Never open any fictitious or unsolicited email attachment even if it comes from a trusted source. Innocent looking emails from apparently trusted source may also contain computer worms, viruses and Trojan programs. Fake websites are often created asking a potential victim to put user id and passwords which eventually makes the job very easy for the attacker. Before opening any email attachment, contact the sender to confirm the message content.
Innumerable cyber attacks happen due to human error. Providing basic training about information security can save an organization from grave security breach. As we believe, workforce is the last line of defense for any company, it is necessary to build a corporate culture that stresses on cyber security safety measures. If the members of an organization are aware of the simple safety measures to keep themselves safe, half the battle is won right there. A company can recover data by spending a huge amount of money, but we must admit that no amount of money can recover the reputation that has been damaged. So, be focused on preventing the attack before it's too late.