Concerned about data security? Bridge the communication gap
Article: Data Security

What are the primary concerns of the top management of business houses? Generally, they are revenue, market shares, economic indicators, competition in the market etc.
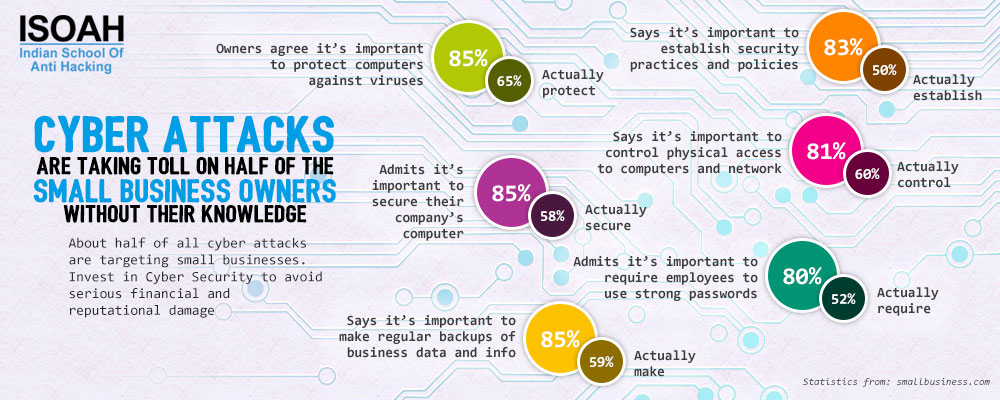
But time has changed. Frequent headlines of sophisticated cyber attacks and data breaches are also a primary concern for big and small corporate houses right now. Hiring cybersecurity specialists is not enough to ward off cyber attacks. According to a new study by IBM, most companies don’t have a formal response plan if they are hit.
According to a research by Ponemon Institute, IT staffs from more than half of business filter out negative facts while reporting security risks to a higher authority. Communication happens usually after a security disaster. In most of the companies, IT security is treated as the concern of IT department or top management. But there is no denying the fact that a cyber attack affects everyone in the enterprise and can bring any organization to its knees by stealing sensitive information or damaging online reputation. Be it a small business house or large corporate giant, data breach can cause the damage of a lot of time, money and reputation.
Security without communication is worthless. In order to bridge the gap, there are few things to remember:
- No matter how great the research is or the pentest or the report or new security policy if no one reads or understands it, it is of no use.
- Complex technical details may not help C-level management to see the big picture. Business leaders typically prefer dashboard like reports that present status and details in easy to understand visual presentations.
- There is a disconnection between different people in a typical organization. The technical team often does not have the language to talk to other disciplines in the company. IT professionals often find it difficult to explain the information or the problem in a format suitable for them. Here, Cyber Security Study Guide created by technical editor Brianne Hughes of security consultancy Bishop Fox, is a solid attempt to bridge the communication gap and establish a shared vocabulary we can build on.
- In most of the cases, people intuitively filter out negative issues before relaying any information to the managers or the boss due to the ‘culture of fear’ that exists in most businesses.
- The lack of communication with the top management regarding the scale of the problem can be solved by fostering a better understanding of the challenges IT security department faces on a day-to-day basis.
Therefore, it must be realized that data security is a joint responsibility between the business and IT that often leads to frustration whereas, it demands collaboration. The target should be helping each other to achieve the goals.
Here are some ways to facilitate better communication:
Be clear about what data needs to be protected:
Any organization deals with bulk of sensitive data. Most IT and development teams are not aware that they are dealing with sensitive data. Here business owners should classify private data and assign access controls. However, these controls do not automatically transfer when data is replicated or transmitted outside the production environment.
The opposite scenario is also present. Shutting down processes in order to protect data is also inhibiting productivity which IT team do not realize while implementing security policies. This can prove to be counterintuitive to business objectives. The collaborative approach can only help to solve the problem.
Use production data in nonproduction environments, and make sure to protect it:
When production data is copied to test a new feature by the development team, there is always a chance of violating data privacy regulation. Some data is private and should always be subject to security precautions, even in test environments. Developers need properly formatted data to test functionally.
There are tools to protect data privacy that allow development teams to conduct work in nonproduction environments. Data masking can be very useful to hide the actual value of data while maintaining its format. For example, actual government ID numbers can be replaced with something with equivalent length and character patterns.
To avoid putting sensitive data at risk in nonproduction environment, consider data discovery and profiling tools. These are programmed to hunt for data that is normally classified as private and can alert in case of any potential risks of exposure.
Understand regulatory and compliance issues and implement best practices:
There are Government and industry regulations related to data privacy. Developers should be aware of the severe legal and financial implications a security breach can have on the business. It would not be wise to wait for a data breach to occur to implement the best practices of data security. Everyone in an organization needs to know and understand the consequences of apparently small actions.
"There's a real gap between the people who find zero days and the people who are affected by them," says Brianne Hughes. Information security is the booming issue of this time but most people are still puzzled about its bizarre and unintuitive landscape. The scenario needs to be changed. Poor communication in an organization is very much responsible for that and it is a security flaw. The organizations must patch this flaw before it gets too late.